The March 2023 SUs address vulnerabilities responsibly reported to Microsoft by security partners and found through Microsoft’s internal processes. Although we are not aware of any active exploits in the wild, our recommendation is to install these updates immediately to protect your environment.
Official announcement can be found here.
Microsoft has released Security Updates (SUs) for vulnerabilities found in:
- Exchange Server 2013
- Exchange Server 2016
- Exchange Server 2019
More details about specific CVEs can be found in the Security Update Guide (filter on Exchange Server under Product Family).
Awareness: Outlook client update for CVE-2023-23397 released
There is a critical security update for Microsoft Outlook for Windows that is required to address CVE-2023-23397. To address this CVE, you must install the Outlook security update, regardless of where your mail is hosted (e.g., Exchange Online, Exchange Server, some other platform). Please see the MSRC blog post about this vulnerability for more details.
But if your mailboxes are in Exchange Online or on Exchange Server, after installing the Outlook update, you can use a script we created to see if any of your users have been targeted using the Outlook vulnerability. The script will tell you if any users have been targeted by potentially malicious messages and allow you to modify or delete those messages if any are found. Please also check script FAQ.
The script will take some time to run, so we recommend prioritizing user mailboxes that are of higher value to attackers (e.g., executives, senior leadership, admins, etc.).
Update installation
The following update paths are available:
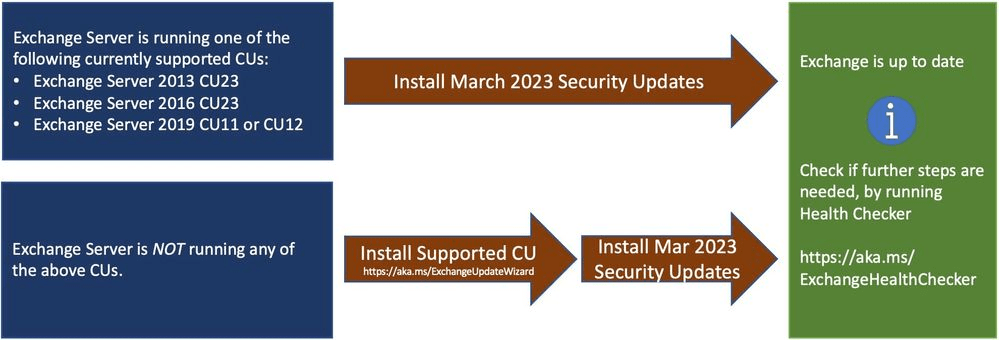
- Install the latest CU. Use the Exchange Update Wizard to choose your current CU and your target CU to get directions.
- Inventory your Exchange Servers to determine which updates are needed using the Exchange Server Health Checker. Running this will tell you if any of your Exchange Servers are behind on updates (CUs, SUs) and if manual actions are needed.
- Always re-run Health Checker after you install an SU to see if any further actions are needed.
- If you encounter errors during or after installation of Exchange Server, run the SetupAssist script. If something does not work properly after updates, see Repair failed installations of Exchange Cumulative and Security updates.
Known issues with this release
- There are no known issues with this release
Issues resolved in this release
- EWS web application pool stops after the February 2023 Security Update is installed – if you have implemented the workaround in the KB article, you should remove the workaround once the March SU is installed (see the KB article for instructions). Running Health Checker will remind you of the need to remove the workaround.
- Exchange Toolbox and Queue Viewer fails after Certificate Signing of PowerShell Serialization Payloa… – this issue has been resolved for servers running the Mailbox role, but this still occurs on servers and workstations that have only the Management Tools role installed.
- This release unblocks customers who can’t enable Extended Protection (EP) because they are using a Retention Policy with Retention Tags that perform Move-to-Archive actions. Note: if you worked around this problem using the updated Exchange Server Extended Protection script, you should roll back the applied IP restrictions after installing this SU by following the script documentation.
- Get-App and GetAppManifests fail and return an exception
- For customers using Exchange Server 2016 or 2019 (with no Exchange 2013) who have non-default applications installed through ECP add-ins, the ECP add-ins page might be broken after February SU is installed
Reach out to Messageware to improve Microsoft Exchange Server Security
If you are not protecting all the protocols used by your Exchange Server, you’re putting your company at a higher risk of a data breach.
Security incidents happen frequently. They cause disruption, loss of data and potentially risk the reputation of your company. However, if you implement these steps, you’re doing more than most other companies.
Have you heard about Messageware’s EPG that offers advanced Exchange Server security to protect organizations from a variety of logon and password attacks, as well as extensive real-time reporting and alerts of suspicious logon activity? Click here to learn more.
