Security researchers confirm Proof-of-Concept (PoC) works against unpatched versions of Microsoft Exchange Server 2013, 2016 and 2019
In early August, researchers discovered cyberattacks against critical infrastructure using two unpublished Exchange Server security vulnerabilities. Microsoft’s Security Research Center (MSRC) stated: “The first exploit identified as CVE-2022-41040, is a Server-Side Request Forgery (SSRF) vulnerability, and the second one, identified as CVE-2022-41082, allows Remote Code Execution (RCE) when PowerShell is accessible to the attacker.” Both CVEs have high severity scores of 8.8 out of 10.
Microsoft recently addressed the two exploits in the November 2022 Patch Tuesday however, many systems remain unpatched and are still being actively targeted. A few days later, security researcher Janggggg uploaded the PoC code to GitHub.
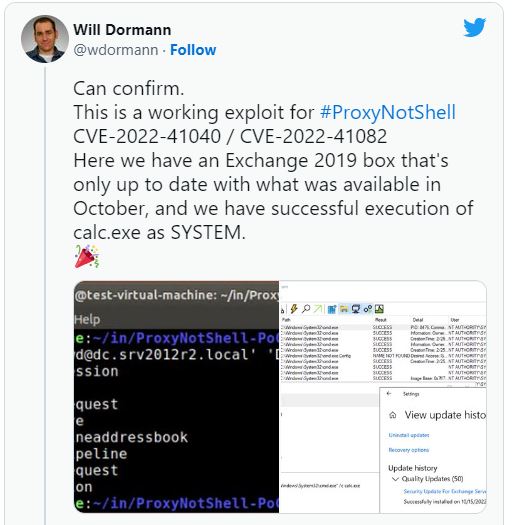
According to Threat intelligence company GreyNoise, ProxyNotShell is still actively being used. In a September 30th post titled Analyzing attacks using the Exchange vulnerabilities CVE-2022-41040 and CVE-2022-41082, Microsoft stated the origin of the attacks could be attributed to a single activity group that is likely state-sponsored.
Microsoft urges its customers to install the updates immediately. Additional information can be found in the November 2022 Exchange Server Security Update Blog.
Reach out to Messageware to improve Microsoft Exchange Server Security
If you are not protecting all the protocols used by your Exchange Server, you’re putting your company at a higher risk of a data breach.
Security incidents happen frequently. They cause disruption, loss of data and potentially risk the reputation of your company. However, if you implement these steps, you’re doing more than most other companies.
Have you heard about Messageware’s EPG that offers advanced Exchange Server security to protect organizations from a variety of logon and password attacks, as well as extensive real-time reporting and alerts of suspicious logon activity? Click here to learn more.
