Outlook Web targeted by Chinese Hacking Group
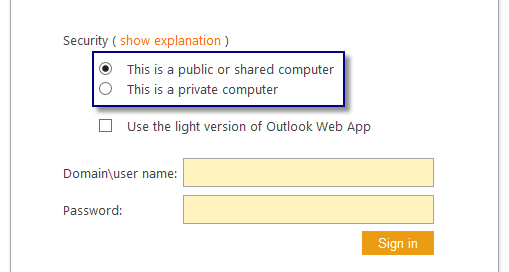
Microsoft confirms that Chinese hackers breached the email accounts of more than two dozen organizations worldwide, including U.S. and Western European government agencies. The attacks were carried out by a threat group tracked as Storm-0558, who used an inactive consumer signing key to create tokens for Azure Active Directory and Microsoft accounts (MSA) to access [...]